I use Let’s Encrypt certificates that are publicly signed, so I don’t have CA, TLS certs and TLS Key. Normally, other MQTT clients allow to set option for “CA signed” certificates, so the PEM files are not needed. I could not find any info on how to generate these PEM files you require from Let’s Encrypt certificates. How can I make this work with your gateway MQTT client?
Hi @roman. @Fomi maybe will answer you most accurate here.
Did you try described cross signing https://letsencrypt.org/certificates/ .
Best regards
Todor
Sorry, I don’t know how Let’s Encrypt certificates work. But I think that those mqtt clients that don’t need a CA certificate may be because they have a built-in CA certificate for the root certificate authority. However, the RAK7240 and RAK7258 do not have a built-in CA certificate. The SSL certificate issued by Let’s Encrypt Certificates also requires a CA certificate. Maybe you can use the Internet to check which CA institution is used by Let’s Encrypt Certifcates and obtain the CA certificate of the institution.
I am learning how Let’s Encrypt works. Regarding “option for CA signed certificates”, can you tell me which mqtt client provides this option? I want to refer to it.
for example: Node-Red, MQTTBox
@yutao, this is not a question specific to Let’s Encrypt, but to any CA using public certificates. Your client needs to interface directly to the public CA to get the certificates without asking for a private key. Writing a private key into a gateway that is deployed into field is almost always a bad security practice.
Does this mean that I need to have the root certificate of all public CAs built into the lora gateway? Or request authentication from a CA agency over the network?
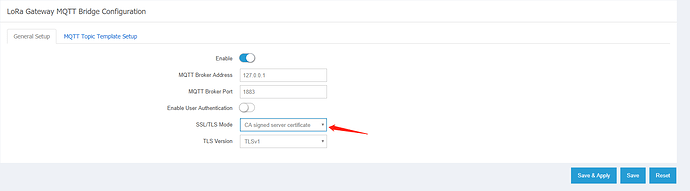
@roman I will try to add a system ca-certificates software to loragateway. Maybe this software can help solve your problem. Do you need to fill in the TLS CERT/TLS KEY, depending on whether the mqtt broker has enabled mutual authentication.
@yutao, the right thing to do is to dynamically get the certificates from the network, as they change often. And, I think it’s best if you provide both options for self-signed and CA certificates, as other MQTT clients do. Some people will want to use self-signed option.
Hi @roman The RAK7249 already supports CA-signed mqtt TLS connections. You can download the latest version for testing on our website. Looking forward to your test results
I already had RAK7249 installed in the field, so it’s difficult to install new firmware now. I don’t have any other one readily available. But, I have RAK833 EVB Kit for testing here. Would it be possible to have a version of firmware that runs on EVB since it’s the same processor module?
I don’t have the firmware for RAK833-EVB. But I think the firmware of the RAK7249 can run on the RAK833-EVB. You can have a try.