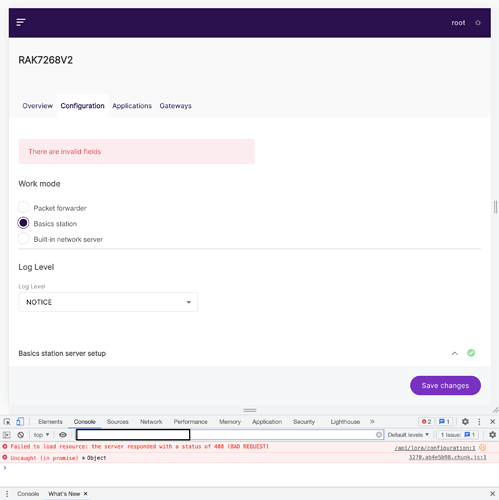
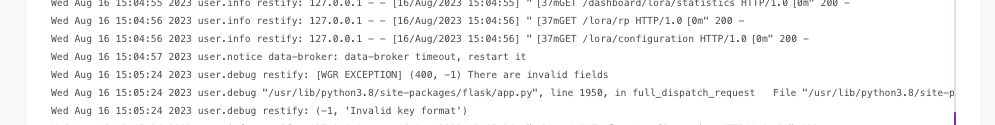
I am trying to setup the new RAK7268V2 Lite with the Senet Network, following directions here: https://docs.senetco.io/dev/gw/RAKMicroBasicsStation/. However, upon trying to set the basic station mode I am getting this error no matter what with the following message “There are invalid fields”. This is what I get in my developer console. I am using version WisGateOS_2.1.2_RAK.
Any update on this or how I might setup this manually without the interface?
Anyone know a solution to this?
We got the same stupid message!
Did everybody solved this issue already?
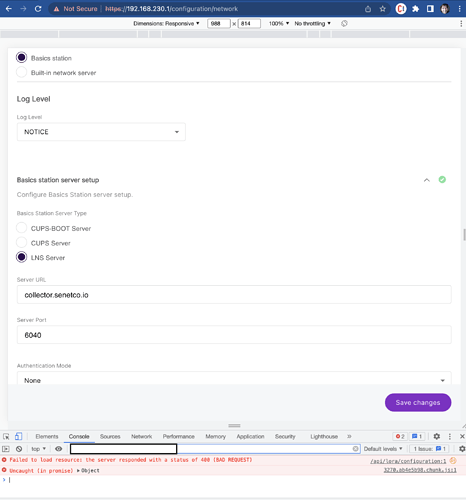
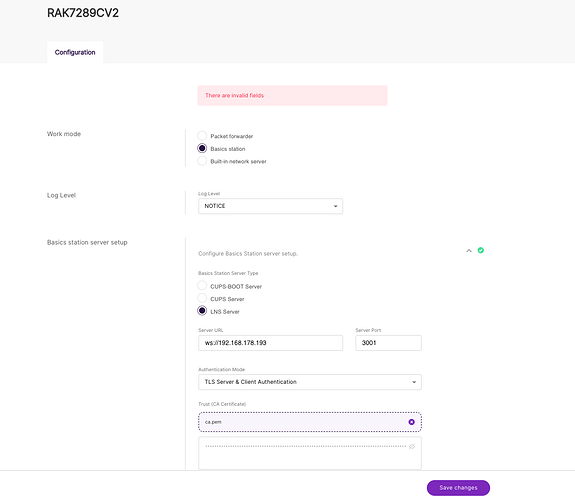
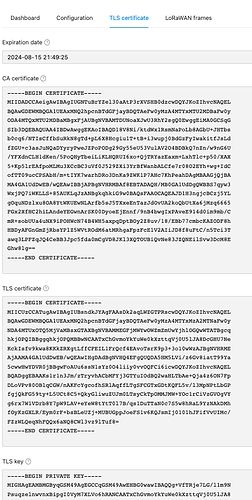
We use RAK7289V2C with Firmeware WisGateOS_2.1.7. All certificates was generated by this repository [chirpstack-certificates] (GitHub - chirpstack/chirpstack-certificates: Scripts to generate certificates for the ChirpStack components.).
We use ChirpStack v4 with Basics station and LNS Server
Hello @s3vdev ,
This error is probably because “ws://192…” and it should be “wss://192…” also this is strange ip for me, is this some kind of locally deployed system?
Best Regards,
Nikola Semov
Thank you for your response.
Yes, it’s our test system with VirtualBox and Debian 11 installed.
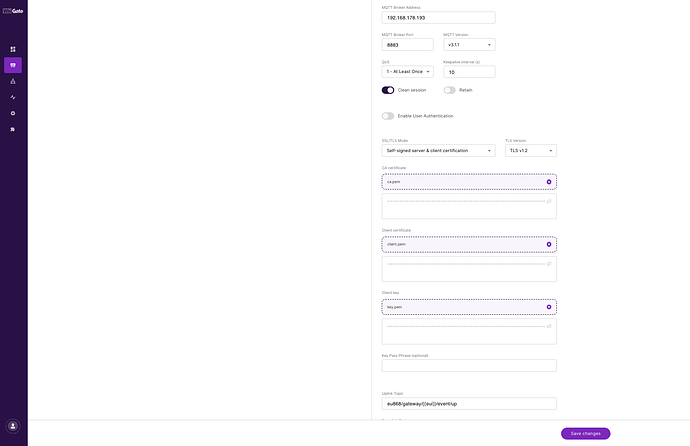
We have already tested the wss://ip:3001 URL. However, after adding the certificates in the basic.station and clicking the update button, the gateway displays the message: “There are invalid fields” 
I have added all the certificates in the TOML files. Using MQTT Explorer, I can test the TLS connection with mqtt://ip:8883. Unfortunately, I am unable to add these certificates to the gateway.
Hello @s3vdev ,
There is a problem with Chirpstack and Basics Station.
We will release firmware version 2.2 which solves the problem in roughly about a month.
Until then you can actually use UDP instead of Basics Station.
Best Regards,
Nikola Semov
Hi Nicola,
Thank you very much. I’ve tested it with both Packet Forwarder and LoRa Gateway MQTT Bridge, following your documentation from here, but I’m encountering the same message:
Do you have any suggestions?
Our Gateway is RAK7289CV2 (16 channels, LTE).
With Packet forwarder and Semtech UDP GWMP Protocol its running good (but without tls).
We’re waiting for the new Firmware Update